Professional Documents
Culture Documents
32 - Bit Microprocessor-Intel 80386
32 - Bit Microprocessor-Intel 80386
Uploaded by
Van Thi Muoi Ngoc NgocOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
32 - Bit Microprocessor-Intel 80386
32 - Bit Microprocessor-Intel 80386
Uploaded by
Van Thi Muoi Ngoc NgocCopyright:
Available Formats
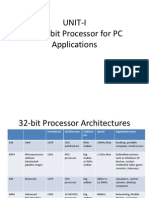
32- bit Microprocessor-Intel
80386
30 Marks
Course Outcome:
Explain memory management and concept of pipelining.
Describe the concept of paging and addressing.
Visit for more Learning Resources
Signal Description of 80386
Signal Descriptions of 80386
• W/R#:The write / read output distinguishes the write and read
cycles from one another.
• D/C#:This data / control output pin distinguishes between a data
transfer cycle from a machine control cycle like interrupt
acknowledge.
• M/IO#:This output pin differentiates between the memory and I/O
cycles.
• LOCK#:The LOCK# output pin enables the CPU to prevent the
other bus masters from gaining the control of the system bus.
• NA#:The next address input pin, if activated, allows address pipelining, during
80386 bus cycles.
• ADS#:The address status output pin indicates that the address bus and bus
cycle definition pins( W/R#, D/C#, M/IO#, BE0# to BE3# ) are carrying the
respective valid signals. The 80383 does not have any ALE signals and so this
signals may be used for latching the address to external latches.
• READY#:The ready signals indicates to the CPU that the previous bus cycle
has been terminated and the bus is ready for the next cycle. The signal is used
to insert WAIT states in a bus cycle and is useful for interfacing of slow devices
with CPU.
• VCC: These are system power supply lines.
• VSS: These return lines for the power supply
• BS16#:The bus size –16 input pin allows the interfacing of 16 bit
devices with the 32 bit wide 80386 data bus. Successive 16 bit bus
cycles may be executed to read a 32 bit data from a peripheral.
• HOLD: The bus hold input pin enables the other bus masters to
gain control of the system bus if it is asserted.
• HLDA: The bus hold acknowledge output indicates that a valid
bus hold request has been received and the bus has been
relinquished by the CPU.
• BUSY#:The busy input signal indicates to the CPU that the
coprocessor is busy with the allocated task.
• ERROR#:The error input pin indicates to the CPU that the
coprocessor has encountered an error while executing its
instruction.
• PEREQ: The processor extension request output signal
indicates to the CPU to fetch a data word for the coprocessor.
• INTR: This interrupt pin is a maskable interrupt, that can be
masked using the IF of the flag register.
• NMI:A valid request signal at the non-maskable interrupt
request input pin internally generates a non-maskable interrupt
of type2.
• RESET: A high at this input pin suspends the current operation
and restart the execution from the starting location.
• N / C: No connection pins are expected to be left open while
connecting the 80386 in the circuit.
Architecture of 80386
Architecture of 80386
• The Internal Architecture of 80386 is divided into 3 sections.
– Central Processing Unit
• Execution Unit
• Instruction Unit
– Memory management unit
• Segmentation
• Paging Unit
– Bus interface unit
• The execution unit consists of the eight 32 bit general
purpose registers (GPR) which are use in physical address
generation, to hold 8 or 16 or 32 bit data and a 64- bit
barrel shifter used to increase the speed of shift, rotate,
multiply and divide operations.
• The instruction unit decodes the op-code of the
instructions which is read from the memory and stores
them in the decoded instruction que for immediate use by
the execution unit during execution.
• The memory Management Unit (MMU) has two sub unit
i.e. Segmentation Unit and Paging Unit.
• Memory is divided into one or more variable length
segments and each 64 Kbytes or 4 Gigabytes in size
depending on memory management techniques used
either segmentation or paging.
• Each task on 80386 can have a maximum of 16,381
segments of up to 4GB each, thus providing 64 TB of
virtual memory to each task.
• In segmentation unit 80386 provides four level protection
for protecting user program and the operating system
from each other.
• The 80386 has three modes of operation:
1. Real Address Mode (Real Mode)
2. Protected Virtual Addressing mode (Protected Mode)
3. Virtual 8086 mode.
• The BIU also offers address pipelining, data bus sizing,
and direct Byte Enable signals for each byte of data bus.
Register of 80386
• The 80386 has 32 registers in the following categories:
– General Purpose Register
– Segment Registers
– Instruction Pointer and Flags
– Status and Control Registers
– System Address Registers
– Debug Registers
– Test Registers
Memory Organization in 80386
• Address Space in 80386
• IO Space in 80386
Real Addressing Modes of 80386
• When processor Reset or Powered up then 80386 is initialized in REAL Mode.
• Real mode has same base architecture as that of 8086, but allows access to
the 32-bit register set of 80386.
• The addressing mechanism, memory size, interrupt handelling , are identical
to Real Mode of the 80286.
• All of the 80386 instructions are available in Real Mode is 16-bits, same as
that of 8086.
• To use 32-bit registers and addressing mmodes, override prefixes ‘E’ must be
used.
• The segment size on the 80386 in Real mode is 64KB so 32-bit effective
addresses must be less than 0000FFFFH.
• The basic Purpose of Real mode in 80386 is to set up the processor for
Protected Mode Operation.
Memory Addressing in Real Mode of 80386
• In Real mode the max. memory size is limited to
1MB, so only address line A2-A19 are used.
• In Real addressing mode the linear addresses are the
same physical addresses as paging is not allowed.
• Physical address is calculated in Real mode by adding
the content of segment register after shifting it left
by four bits with an effective address and generates a
physical address. Which is compatible with 80286
Real Mode.
• All address in Real Mode should not more than
64KB in size and may be Read, written or executed.
• The 80386 generates an exception 13 if a data
operand or instruction fetch occurs past the end of
a segment.
• Segment may be overlapped in Real mode means if
a particular segment does not use all 64KB another
segment can be override on top of the unused
portion of the previous segment.
• Hence, this allows the programmer to minimize the
amount of physical memory needed for a program.
Protected Virtual Address Mode (PVAM) of
80386
• When the processor operates in protected virtual address
mode i.e. Protected Mode then the complete capabilities
of the 80386 are used.
• Protected mode is used to increase the linear address
space up to 4GB and used to execute virtual memory
programs of the size of 64TB.
• Also Protected mode of 80386 is used to run all the existing
8086 and 80286 program with a memory management and
protection mechanism.
• Protected mode of 80386 also supports the use of
additional instructions for supporting multitasking OS.
• The linear address is then either used as the 32- bit
physical address, or the paging mechanism maps the 32-
bit linear address into a 32 bit physical address if paging is
enabled.
• In protected mode the selector is used as an index for
system define table such as LDT or GDT
• The LDT or GDT table contains 32 bit base address of given
segment.
• The physical address is formed by adding the base address
obtained from the table to offset.
• Paging provides additional memory management
mechanism which operates only in Protected mode and
managing the very large segments of the 80386.
Segment Descriptor Cache
• Every segment register has a segment descriptor
cache register.
• Selector fields: In protected mode of 80386, a selector
has three fields i.e. Table indicator (TI) which is used to
points either a Local or Global descriptor table,
descriptor entry index (Index) and Requestor Privilege
Level (RPL) as shown in fig.
• The TI bit is used to select one of two tables of
descriptors. i.e. GDT and if TI bit is 0
• And TI is 1 then LDT
• The Index is used to selects one of 8KB
descriptors entry in appropriate descriptor
table.
• The RPL (Requestor Privilege Level) bits are
used for testing of the selector’s privilege
attributes.
Descriptor Attributes Bits
Detailed Format of Segments Descriptor
cache Register
• Segment Descriptor Cache in Real Mode: Internal
Privilege level is always fixed to highest level, level 0, so
I/O and other privilrged op-codes can be executed.
• Segment Descriptor Cache in Protected Mode: All fields
are defined by the content of segment descriptor pointed
by the selector index value in the segment register.
• Segment Descriptor Cache in Virtual Mode: The virtual
program executes at lowest privilege level, i.e. level 3, to
allow trapping of all IOPL sensitive instructions and level-0
only instruction.
Difference between Real and Protected
Mode
Real Mode Protected Mode (PVAM)
Memory addressing up to 1 MB physical Memory addressing up to 16 MB of
memory physical memory
No virtual memory support Supports up tp to 64TB of virtual memory
Memory Protection mechanism is not Memory Protection Mechanism is avilable
available
Does not support virtual address space Gives virtual and physical address space
Does not support LDT and GDT Supports LDT and GDT
Segment descriptor cache is not available Segment descriptor cache is available
Supports Segmentation Supports segmentation and paging.
Segmentation
• Segmentation is memory management technique with
protection.
• The information of the segment is stored in an 8 byte
format called as descriptor.
• There are three types of descriptor table:
– LDT
– GDT
– IDT
• LDT, GDT and IDT are of variable length memory size
table which ranges between 8 bytes and 64KB.
• Each table content maximum 8K od 8byte
descriptors and the upper 13 bits of selectors
are used as an index for the descriptor table.
• These tables have registers associated with
them which hold the 32-bit linear base
address and the 16- bit limit of each table and
these registers are LDTR, GDTR and IDTR.
Protection Levels in 80386
• The 80386 supports four protection which isolates and
protect user programs for each other and the operating
system during a multi-tasking operating system.
• The protection level avoid the use of privileged
instructions, I/O instructions and access to segments
and segment descriptors.
• The privilege protection mechanism of 80386 is
integrated in On- chip Memory Management Unit
which also gives protection to pages, when paging is
enable.
Privilege levels in 80386
A. Task Privilege level:
• At any point in time, a task in 80386 always executes at one
of four Privilege levels.
• The current privilege level of selector is indicated by the
RPL field. i.e. the two least significant bits of the selector.
B. Selector Privilege (RPL):
• The privilege level of selector is indicated by the RPL field
i.e. two least significant bits of the selector.
• RPL of selector is used only to test requestor privilege level
with current privilege level of a segment to be used called
effective privilege level i.e. EPL
Virtual 8086 mode for executing 80386 Programs
• The 80386 allows the execution of 8086 program in
both Real Mode and Virtual 8086 mode i.e. Virtual
Mode.
• Virtual 8086 mode provides the system designer the
most flexibility out of two modes i.e Real and
PVAM.
• The virtual mode allows the execution 8086
programs, by taking full advantage of the 80386
protection mechanism.
• Hence, it allows the simultaneous exection of 8086
OS with its application, and 80386 OS, both 80286
and 80386 applications.
Virtual 8086 Mode Addressing Mechanism
• The major difference between 80386 Real and Protected
mode is the way that segment selectors are interpreted.
• When the processor is operating in Virtual Mode the
segment registers are used in an identical to Real Mode.
• The content of the segment register are shifted towards
left by 4 bits and added to the offset to form the
segment base linear address.
• The 80386 gives facility to the OS for specifying which
programs use 8086 style address mechanism, and which
program use Protected mode addressing on a per task
basis.
• By the use of paging memory management,
the one MB address space of virtual mode
task can be mapped anywhere in the 4 GB of
linear address space of 80386.
• Virtual mode effective address i.e. segment
offsets that exceed 64KB will cause an
exception 13 as in Real mode.
For more detail contact us
You might also like
- Architecture of 80386Document39 pagesArchitecture of 80386Satish KedarNo ratings yet
- Architecture of 80386Document39 pagesArchitecture of 80386Imran KhanNo ratings yet
- Architecture of 80386Document39 pagesArchitecture of 80386Jaimon JacobNo ratings yet
- Architecture of 80386 MicroproDocument39 pagesArchitecture of 80386 Microproompa13No ratings yet
- Microprocessor 80386Document40 pagesMicroprocessor 80386eshwar_worldNo ratings yet
- Architecture of 80386Document39 pagesArchitecture of 80386Raj KumarNo ratings yet
- Architecture of 80386 MicroproDocument40 pagesArchitecture of 80386 MicroproajayNo ratings yet
- Unit - Iv: Advanced Microprocessors: Salient Features of 80386Document14 pagesUnit - Iv: Advanced Microprocessors: Salient Features of 80386Swamy NallabelliNo ratings yet
- Architecture of 80386 MicroproDocument39 pagesArchitecture of 80386 MicroproDeepthiNo ratings yet
- The Complete Understanding of Microprocessors and Intro To ARMDocument56 pagesThe Complete Understanding of Microprocessors and Intro To ARMasimNo ratings yet
- MP-MC R16 - Unit-4Document14 pagesMP-MC R16 - Unit-4satyanarayana12No ratings yet
- Advanced MicroprocessorDocument43 pagesAdvanced MicroprocessorbhavithakandulareddyNo ratings yet
- FEATURES OF 80386:: 2) Address 4GB of Memory 2) 16 MB ofDocument39 pagesFEATURES OF 80386:: 2) Address 4GB of Memory 2) 16 MB ofJ VNo ratings yet
- Architecture of 80386Document42 pagesArchitecture of 80386santosh.parsaNo ratings yet
- NotesDocument21 pagesNotesShinisg Vava50% (2)
- FEATURES OF 80386:: 3) Address 4GB of Memory 3) 16 MB ofDocument39 pagesFEATURES OF 80386:: 3) Address 4GB of Memory 3) 16 MB ofSorabh ChhabraNo ratings yet
- 8086 Third Term TopicsDocument46 pages8086 Third Term TopicsgandharvsikriNo ratings yet
- Microprocessor 80386Document17 pagesMicroprocessor 80386gujusNo ratings yet
- Features of 80386Document13 pagesFeatures of 80386Aswathy CjNo ratings yet
- Real-Mode and Protected-Mode Memory AddressingDocument13 pagesReal-Mode and Protected-Mode Memory AddressingPriya DarshiniNo ratings yet
- G MPMC U4 Rit 150 CopiesDocument19 pagesG MPMC U4 Rit 150 CopiesBobby SatyaNo ratings yet
- MP Unit-8 VtuDocument10 pagesMP Unit-8 VtuBmvpNo ratings yet
- MPMC M-2 U-4Document21 pagesMPMC M-2 U-4Krishna BoreddyNo ratings yet
- Microprocessors & Interfacing - (Ch3-Sec3A) - 80 X 86 Processor ArchitectureDocument24 pagesMicroprocessors & Interfacing - (Ch3-Sec3A) - 80 X 86 Processor ArchitectureSainadh PolavarapuNo ratings yet
- 80386Document89 pages80386chandanayadav849050% (2)
- Unit-I: - 80386 IntroductionDocument74 pagesUnit-I: - 80386 IntroductionOmkar MarkadNo ratings yet
- Lecture#2 Fut Microprocessor PDFDocument81 pagesLecture#2 Fut Microprocessor PDFAhmedGamalNo ratings yet
- Unit 1 - 80386 Architecture and Programmers ModelDocument43 pagesUnit 1 - 80386 Architecture and Programmers ModelpjNo ratings yet
- 32 - Bit Microprocessor-Intel 80386Document71 pages32 - Bit Microprocessor-Intel 80386Ibtisam Anwar KhattakNo ratings yet
- 68 XXXDocument20 pages68 XXXRyan John de LaraNo ratings yet
- Pentium ProcessorDocument18 pagesPentium ProcessorRabab Khan RongonNo ratings yet
- Document 2Document4 pagesDocument 2Abdulrafay SaimNo ratings yet
- Mod 3 - 80386 and PentiumDocument7 pagesMod 3 - 80386 and PentiumAlenNo ratings yet
- and 80486Document28 pagesand 80486sangeetaranjan0% (1)
- Pentium ArchitectureDocument18 pagesPentium ArchitectureMary HarrisonNo ratings yet
- Advanced ProcessorDocument85 pagesAdvanced ProcessorRenit AntoNo ratings yet
- Advanced Microprocessors: Presented by Ashish Kumar Singh Pranav Gautam Guide Mrs. Nayanica SrivastavaDocument20 pagesAdvanced Microprocessors: Presented by Ashish Kumar Singh Pranav Gautam Guide Mrs. Nayanica SrivastavaPranav GautamNo ratings yet
- Chapter 2: The Microprocessor and Its ArchitectureDocument108 pagesChapter 2: The Microprocessor and Its ArchitectureTaqsim RajonNo ratings yet
- Final ENCE 455 - ADVANCED MICROPROCESSOR SYSTEMS AND INTERFACING EXAMS - NOV 2021Document8 pagesFinal ENCE 455 - ADVANCED MICROPROCESSOR SYSTEMS AND INTERFACING EXAMS - NOV 2021Crentsil KwayieNo ratings yet
- Microprocessor ArchitectureDocument23 pagesMicroprocessor Architectureganesh6583No ratings yet
- 80186Document24 pages80186a_charaniaNo ratings yet
- Intel: Term Paper On 80486 MicroprocessorDocument8 pagesIntel: Term Paper On 80486 MicroprocessorLALRAZNo ratings yet
- 1-32-Bit Microprocessor - Intel 80386Document37 pages1-32-Bit Microprocessor - Intel 80386afzal_a67% (3)
- MPMC NotesDocument118 pagesMPMC NotesNivvi NivethaNo ratings yet
- 80386Document84 pages80386SridharNo ratings yet
- 80286, 80386, 80486 and Pentium MicroprocessorDocument9 pages80286, 80386, 80486 and Pentium Microprocessoramit mahajan91% (11)
- MPS Lecture 3 - The Microprocessor and Its ArchitectureDocument26 pagesMPS Lecture 3 - The Microprocessor and Its ArchitectureShehroze TalatNo ratings yet
- MICRO133 Prelim Lecture 3 Intel 80286 and 80386 Microprocessor Protected Mode Addressing v2Document60 pagesMICRO133 Prelim Lecture 3 Intel 80286 and 80386 Microprocessor Protected Mode Addressing v2John Vinz CustodioNo ratings yet
- Contents:: Salient Features of 80386 Functional Block Diagram of 80836 Pin Description of 8086Document26 pagesContents:: Salient Features of 80386 Functional Block Diagram of 80836 Pin Description of 8086ajayNo ratings yet
- Architecture of 80286 80386 80486 MicroproseccorsDocument91 pagesArchitecture of 80286 80386 80486 MicroproseccorsYash Mistry100% (1)
- and Pentium MicroprocessorsDocument37 pagesand Pentium Microprocessorsgayathrishiv91100% (1)
- The Microprocessor & Its Architecture: by Engr: Shah Rehan AliDocument39 pagesThe Microprocessor & Its Architecture: by Engr: Shah Rehan AliUsman SaeedNo ratings yet
- Advanced Microprocessors-80286Document12 pagesAdvanced Microprocessors-80286Aaron BrooksNo ratings yet
- Unit 1Document48 pagesUnit 120IF207 Gayatri PatilNo ratings yet
- Microprocessor NotesDocument140 pagesMicroprocessor NotesSaquibh ShaikhNo ratings yet
- Unit IV Computer ArchitectureDocument18 pagesUnit IV Computer Architecturevaishnavi sharmaNo ratings yet
- 3rd Unit FinalDocument80 pages3rd Unit FinalTARANNo ratings yet
- Microprocessor Unit OneDocument21 pagesMicroprocessor Unit OneUtshab ChapagainNo ratings yet
- Preliminary Specifications: Programmed Data Processor Model Three (PDP-3) October, 1960From EverandPreliminary Specifications: Programmed Data Processor Model Three (PDP-3) October, 1960No ratings yet
- Practical Reverse Engineering: x86, x64, ARM, Windows Kernel, Reversing Tools, and ObfuscationFrom EverandPractical Reverse Engineering: x86, x64, ARM, Windows Kernel, Reversing Tools, and ObfuscationNo ratings yet
- Trainer Digital Elect KMS-01ADocument2 pagesTrainer Digital Elect KMS-01ASaridi SaliminNo ratings yet
- Algorithm State Machine: Circuits and Control Circuits. Data Path Circuits Perform The Functions Such AsDocument12 pagesAlgorithm State Machine: Circuits and Control Circuits. Data Path Circuits Perform The Functions Such Asabuzar rao100% (1)
- Akbar 2011Document10 pagesAkbar 2011kamarajme2006No ratings yet
- Advantages and Disadvantages of Finfets - AlyaaDocument12 pagesAdvantages and Disadvantages of Finfets - AlyaaAlyaa Nadzirah Binti ShbiniNo ratings yet
- M6Me Pentium Pro Pci/Eisa: System Board ManualDocument87 pagesM6Me Pentium Pro Pci/Eisa: System Board ManualRoccotronNo ratings yet
- Inventec Laptop Motherboard Schematic DiagramDocument70 pagesInventec Laptop Motherboard Schematic Diagrampukymotto100% (1)
- Microcontrollers and ApplicationsDocument254 pagesMicrocontrollers and ApplicationsArivukkarasan RajaNo ratings yet
- The Full Guide of Best USB Flash Drive Repair SoftwareDocument29 pagesThe Full Guide of Best USB Flash Drive Repair SoftwareHacene LamraouiNo ratings yet
- Logical Efforts-Good ReadDocument71 pagesLogical Efforts-Good ReadProf. Vikas BalikaiNo ratings yet
- XeLLous JTAG Noob Friendly PDFDocument11 pagesXeLLous JTAG Noob Friendly PDFViorel AldeaNo ratings yet
- Module 4 Extra Problems On CacheDocument43 pagesModule 4 Extra Problems On CacheLalala LandNo ratings yet
- Via Via Prosavageddr Km266 Prosavageddr Km266 Chipset Introduction Chipset IntroductionDocument16 pagesVia Via Prosavageddr Km266 Prosavageddr Km266 Chipset Introduction Chipset IntroductionVla VcgNo ratings yet
- Sistem Kunci Pintu Otomatis Menggunakan Rfid: Nama: Muh. Fachrul Alam NIM: D42116520Document4 pagesSistem Kunci Pintu Otomatis Menggunakan Rfid: Nama: Muh. Fachrul Alam NIM: D42116520Sulthan ANNo ratings yet
- SCL Logic Synthesis ReportDocument10 pagesSCL Logic Synthesis ReportAishwarya a nairNo ratings yet
- MOSFET Leakage PowerDocument47 pagesMOSFET Leakage PowerRamakrishnaRao SoogooriNo ratings yet
- Introduction To Microprocessors Dual-Inline PackDocument12 pagesIntroduction To Microprocessors Dual-Inline Packi studyNo ratings yet
- Debugger Hc12Document52 pagesDebugger Hc12carver_uaNo ratings yet
- Adam 6066Document16 pagesAdam 6066Cosme RodolfoNo ratings yet
- COA-BEC306C Assingments-2Document1 pageCOA-BEC306C Assingments-2Savitri HalakarniNo ratings yet
- Practical Work 6 - CMOS + Rubrics PDFDocument10 pagesPractical Work 6 - CMOS + Rubrics PDFRiki SmithNo ratings yet
- 2 Megabit (256 K X 8-Bit) CMOS EPROM: Distinctive CharacteristicsDocument12 pages2 Megabit (256 K X 8-Bit) CMOS EPROM: Distinctive CharacteristicsVictor TruccoNo ratings yet
- Computer Fundamental IndiaBixDocument162 pagesComputer Fundamental IndiaBixNa Thaka83% (6)
- Storage NotesDocument12 pagesStorage NotesJoemon JoseNo ratings yet
- Computer Hardware: PeripheralsDocument6 pagesComputer Hardware: PeripheralsDienizs Labini TadenaNo ratings yet
- Ha and FaDocument11 pagesHa and FaManoj KumarNo ratings yet
- HDD GURU FORUMS - View Topic - Dumping Micron M500 SSD Firmware MU05Document12 pagesHDD GURU FORUMS - View Topic - Dumping Micron M500 SSD Firmware MU05Nauka SolutionNo ratings yet
- BiCMOS Advantages PDFDocument2 pagesBiCMOS Advantages PDFPratibha SinghNo ratings yet
- XT532 DatasheetDocument1 pageXT532 DatasheetRehan ShaikhNo ratings yet
- Grade8 - Q0 - W4 - PerformMensuration - FOR TEACHERDocument35 pagesGrade8 - Q0 - W4 - PerformMensuration - FOR TEACHERErika Arcega100% (2)
- P150SM EsmDocument126 pagesP150SM EsmNuno AlmeidaNo ratings yet