Professional Documents
Culture Documents
XDR (Extended Detection and Response) : Uses of XDR in AI
XDR (Extended Detection and Response) : Uses of XDR in AI
Uploaded by
amit.andre81440 ratings0% found this document useful (0 votes)
4 views6 pagesOriginal Title
XDR
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
4 views6 pagesXDR (Extended Detection and Response) : Uses of XDR in AI
XDR (Extended Detection and Response) : Uses of XDR in AI
Uploaded by
amit.andre8144Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 6
XDR (Extended Detection and Response)
Uses of XDR in AI:
Uses of XDR in AI Description
Using XDR to feed AI models with comprehensive security data,
AI-Driven Threat
enabling predictive analytics for identifying and mitigating future
Prediction
threats based on patterns and anomalies.
Autonomous Incident Leveraging XDR's integration capabilities to allow AI to
Response and automatically respond to and remediate threats without human
Remediation intervention, reducing response times significantly.
Employing XDR to provide AI with detailed data across networks
Deep Behavioural
and endpoints, enabling deep analysis of user and entity behaviour
Analysis
to detect sophisticated, hidden threats.
Cross-Domain Utilizing XDR to aggregate security data, allowing AI to conduct
Vulnerability comprehensive vulnerability assessments across different domains
Assessment and environments, enhancing overall security posture.
Integrating XDR with AI to improve DLP strategies by analysing
AI-Optimized Data
vast amounts of data to identify and protect against sophisticated
Loss Prevention (DLP)
data exfiltration attempts.
Combining XDR's data collection capabilities with AI to detect
Enhanced Anomaly
anomalies across various vectors with higher accuracy and speed,
Detection
leading to faster identification of unknown threats.
Using XDR as a basis for AI to proactively hunt for emerging cyber
Predictive Cyber
threats by analysing trends and predicting where vulnerabilities may
Threat Hunting
be exploited before they are attacked.
Leveraging the comprehensive view provided by XDR to train AI
Advanced Fraud
models in detecting complex and sophisticated fraud patterns across
Detection
various platforms and transaction types.
AI-Enabled Employing XDR data to feed AI systems for continuous and
Compliance automated compliance monitoring, ensuring that an organization's
Monitoring security practices meet regulatory requirements across all vectors.
Utilizing XDR to gather security data for AI analysis, which can
Intelligent Security
then provide recommendations for optimizing security policies and
Policy Optimization
configurations in real-time, adapting to evolving threat landscapes.
Autonomous Incident Response and Remediation:
AI-Driven Threat Prediction:
Deep Behavioural Analysis:
Library is used in implementation of Microsoft XDR:
Microsoft XDR (Extended Detection and Response) uses a combination of libraries and technologies
for its implementation, including:
o Azure Sentinel: Microsoft's cloud-native SIEM (Security Information and Event
Management) platform that serves as the central hub for XDR.
o Azure Monitor: Azure's monitoring service that collects and analyzes data from various
sources, including security logs.
o Azure Machine Learning: Azure's cloud-based machine learning service that provides
algorithms and tools for building and deploying ML models.
o Azure Cognitive Services: Azure's suite of AI services that includes natural language
processing, computer vision, and speech recognition capabilities.
o Microsoft Graph Security API: An API that provides access to security-related data from
Microsoft 365 and other Microsoft services.
o Python: A widely used programming language for data analysis, machine learning, and
automation.
o C#: A programming language primarily used for developing applications on the Microsoft
.NET platform.
o PowerShell: A scripting language and command-line shell designed for system administration
and automation tasks.
o Open Source Libraries: XDR also leverages open source libraries such as Elasticsearch,
Logstash, and Kibana for data ingestion, storage, and visualization.
Additionally, XDR integrates with various third-party security solutions and technologies through its
open APIs and connectors. This allows organizations to extend the capabilities of XDR and tailor it to
their specific security needs.
Build XDR:
Building an Extended Detection and Response (XDR) platform requires a combination of technology,
expertise, and a well-defined strategy. Here are the key steps involved:
1. Define Your XDR Strategy:
o Determine the scope and objectives of your XDR platform.
o Identify the specific security use cases you want to address, such as threat detection, incident
response, and threat hunting.
o Establish performance metrics and goals for your XDR platform.
2. Select and Implement Core Technologies:
o Choose a cloud-based SIEM platform that serves as the central hub for collecting and
analysing security data.
o Integrate with endpoint detection and response (EDR) solutions to monitor and protect
endpoints.
o Implement network detection and response (NDR) capabilities to monitor and analyse
network traffic for threats.
o Consider adding threat intelligence feeds and threat hunting tools to enhance detection and
investigation capabilities.
3. Build and Deploy Detection and Response Playbooks:
o Define automated playbooks that outline the steps to be taken when specific security events or
threats are detected.
o Use machine learning and artificial intelligence (AI) to enhance the accuracy and efficiency
of threat detection.
o Establish clear escalation procedures and communication channels for incident response.
4. Integrate with Existing Security Tools:
o Connect your XDR platform with existing security tools, such as firewalls, intrusion detection
systems (IDS), and vulnerability scanners.
o Use open APIs and connectors to facilitate integration and data sharing.
o Leverage security orchestration, automation, and response (SOAR) tools to automate security
tasks and streamline incident response.
5. Train and Staff Your Team:
o Provide training to your security team on the XDR platform and its capabilities.
o Ensure your team has the necessary skills and expertise to effectively operate and manage the
platform.
o Consider outsourcing some aspects of XDR operations to a managed security service provider
(MSSP) if needed.
6. Monitor and Evaluate Your XDR Platform:
o Regularly monitor the performance of your XDR platform and make adjustments as needed.
o Evaluate the effectiveness of your detection and response playbooks and update them based
on lessons learned.
o Track key metrics and report on the overall effectiveness of your XDR program.
Additional Considerations:
o Data Privacy and Compliance: Ensure your XDR platform complies with relevant data
privacy regulations and industry standards.
o Scalability and Performance: Choose a platform that can handle the volume and complexity
of your security data.
o Cost Optimization: Consider the cost of implementing and maintaining your XDR platform,
including licensing fees, infrastructure costs, and staffing requirements.
o Vendor Support: Select a vendor that provides reliable support and ongoing updates for their
XDR platform.
Libraries for Building an XDR Platform with AI:
1. Data Analysis and Machine Learning:
o Python: A widely used programming language for data analysis, machine learning, and
automation.
o scikit-learn: A comprehensive Python library for machine learning algorithms and data pre-
processing.
o TensorFlow: A popular open-source machine learning library developed by Google.
o PyTorch: Another popular open-source machine learning library known for its flexibility and
ease of use.
2. Security Data Analysis:
o Splunk: A commercial software platform for collecting, analysing, and visualizing security
data.
o Elasticsearch: An open-source search and analytics engine commonly used for security data
analysis.
o Logstash: An open-source data collection and processing pipeline for security data.
o Kibana: An open-source data visualization tool for Elastic search.
3. Threat Intelligence:
o MISP: An open-source threat intelligence platform for sharing and analysing threat data.
o OpenCTI: An open-source threat intelligence platform focused on structured data analysis.
o Anomaly Threat Stream: A commercial threat intelligence platform that provides access to a
global threat database.
4. Security Orchestration and Automation:
o Demisto: An open-source security orchestration and automation platform.
o IBM Resilient: A commercial security orchestration and automation platform.
o ServiceNow Security Operations: A cloud-based security orchestration and automation
platform.
5. Chatbot’s and Virtual Assistants:
o Dialogflow: A Google-developed platform for building natural language Chatbot’s.
o Amazon Lex: An Amazon Web Services (AWS) platform for building Chatbot’s and virtual
assistants.
o Microsoft Bot Framework: A Microsoft platform for building and deploying chatbots and
virtual assistants.
Future Uses of XDR in Artificial Intelligence (AI):
1. Predictive Threat Intelligence with Generative AI: Use generative AI models to create
synthetic threat data and enhance the training of AI-powered threat detection models.
2. AI-Driven Security Orchestration and Automation: Develop AI algorithms to optimize the
orchestration and automation of security tasks, improving efficiency and response times.
3. Cognitive Security Analytics: Leverage cognitive AI techniques to understand the context and
intent behind security events, enabling more accurate and timely decision-making.
4. AI-Assisted Incident Triage and Prioritization: Use AI to automatically triage and prioritize
security incidents based on their potential impact and urgency, guiding security teams to focus on the
most critical threats.
5. AI-Powered Vulnerability Management: Enhance vulnerability management by using AI to
identify and prioritize vulnerabilities based on their exploitability and potential impact.
6. AI-Enabled Threat Hunting and Forensics: Develop AI algorithms to automate threat hunting
and forensic analysis, reducing the time and effort required to detect and investigate advanced threats.
7. AI-Driven Security Risk Assessment: Use AI to assess security risks and identify potential
vulnerabilities in real-time, enabling organizations to proactively mitigate threats.
8. AI-Assisted Insider Threat Detection: Leverage AI to analyse user behaviour patterns and
identify anomalies that may indicate malicious insider activity.
9. AI-Powered Compliance Monitoring: Use AI to monitor compliance with security regulations
and standards, ensuring continuous adherence and reducing the risk of penalties.
10. AI-Enabled Security Awareness Training: Develop AI-powered security awareness training
programs that are personalized and adaptive, improving employee understanding of security best
practices.
You might also like
- Best Android Tools For SniffingDocument13 pagesBest Android Tools For SniffingVladimir Calle MayserNo ratings yet
- Sohail Sajid: (US Citizen) Cyber Security EngineerDocument7 pagesSohail Sajid: (US Citizen) Cyber Security EngineerAshwani kumarNo ratings yet
- Microsoft Defender SuiteDocument15 pagesMicrosoft Defender SuitePenny worthNo ratings yet
- Awesome Penetration Testing DocumentationDocument32 pagesAwesome Penetration Testing DocumentationRizam Ali JavedNo ratings yet
- Interpersonal Relationships Professional Communication Skills For Nurses 7nbsped 9780323242813 0323242812Document576 pagesInterpersonal Relationships Professional Communication Skills For Nurses 7nbsped 9780323242813 0323242812monikaretnowatiNo ratings yet
- Essentials of Application SecurityDocument56 pagesEssentials of Application Securityankit0703No ratings yet
- Cybersecurity AssessmentDocument26 pagesCybersecurity AssessmentRio Nguyen50% (2)
- Appian BPMSuiteDocument22 pagesAppian BPMSuiteamit.andre8144No ratings yet
- SIEMvsEDR PDFDocument10 pagesSIEMvsEDR PDFOverereNo ratings yet
- Cortex XDRDocument6 pagesCortex XDRStacy Marie100% (1)
- Fundamentals of Curriculum DesignDocument19 pagesFundamentals of Curriculum DesignNemalyn Arizala BasasNo ratings yet
- ASME V Article 10 Leak TestingDocument2 pagesASME V Article 10 Leak TestingAmanda Ariesta Aprilia0% (1)
- Login & PasswordsDocument1 pageLogin & Passwordsamit.andre8144No ratings yet
- 06-21 SolutionBrief V10.disarmedDocument5 pages06-21 SolutionBrief V10.disarmedramramNo ratings yet
- Test Initial Engleza Clasa A 6 ADocument2 pagesTest Initial Engleza Clasa A 6 AAlexa Blanka100% (3)
- Perkembangan Kurikulum Di IndonesiaDocument22 pagesPerkembangan Kurikulum Di IndonesiaRhia SartikaNo ratings yet
- European Day of LanguagesDocument13 pagesEuropean Day of LanguagesAlex Adriana RaduNo ratings yet
- UntitledDocument10 pagesUntitledamit.andre8144No ratings yet
- Understanding Atheism Relationship Betwe PDFDocument195 pagesUnderstanding Atheism Relationship Betwe PDFAily SangcapNo ratings yet
- CybersecurityDocument11 pagesCybersecurityPragati ChaturvediNo ratings yet
- Cortex XDR: Safeguard Your Entire Organization With The Industry's First Extended Detection and Response PlatformDocument8 pagesCortex XDR: Safeguard Your Entire Organization With The Industry's First Extended Detection and Response PlatformOmar OchoaNo ratings yet
- Cortex XDR: Safeguard Your Entire Organization With The Industry's First Extended Detection and Response PlatformDocument8 pagesCortex XDR: Safeguard Your Entire Organization With The Industry's First Extended Detection and Response PlatformvlimbadiNo ratings yet
- Palo Alto Cortex XDRDocument8 pagesPalo Alto Cortex XDRfahid.shopupNo ratings yet
- Cortex XDR: Safeguard Your Entire Organization With The Industry's First Extended Detection and Response PlatformDocument7 pagesCortex XDR: Safeguard Your Entire Organization With The Industry's First Extended Detection and Response PlatformAmanuelNo ratings yet
- Percept XDR - Datasheet - 21Document5 pagesPercept XDR - Datasheet - 21Arita DalalNo ratings yet
- Safeguarding The Business With SIEM and XDRDocument17 pagesSafeguarding The Business With SIEM and XDRhim2000himNo ratings yet
- QRadar XDR - IBM DocumentationDocument4 pagesQRadar XDR - IBM DocumentationWorku BayuNo ratings yet
- Palo Alto Network Cortex XDRDocument6 pagesPalo Alto Network Cortex XDRKhanwoodNo ratings yet
- Cortex XDR: Defining The New Category of Enterprise-Scale Prevention, Detection, and ResponseDocument6 pagesCortex XDR: Defining The New Category of Enterprise-Scale Prevention, Detection, and ResponseSaul Vilca VillenaNo ratings yet
- Plagiarism Report 1000 PDFDocument4 pagesPlagiarism Report 1000 PDFBuddhu MotsNo ratings yet
- Detect Track Security Attacks Netwitness Rsa 40100Document22 pagesDetect Track Security Attacks Netwitness Rsa 40100shadNo ratings yet
- XDR Buyers Guide 2023 Edition 1Document19 pagesXDR Buyers Guide 2023 Edition 1vethNo ratings yet
- Open XDR Vs SIEMDocument5 pagesOpen XDR Vs SIEMHangup9313No ratings yet
- RF Analyst Lab ExamDocument5 pagesRF Analyst Lab ExamGhanshyam SawainyaNo ratings yet
- Attemp 2 - Master User ProtectionDocument12 pagesAttemp 2 - Master User ProtectionHaikal DzulfikriNo ratings yet
- EnglishDocument1 pageEnglishMark Wendel PacotNo ratings yet
- AI in DefenceDocument12 pagesAI in DefenceKavyaNo ratings yet
- 10-21 NDR BuyersGuide V6.disarmedDocument7 pages10-21 NDR BuyersGuide V6.disarmedramramNo ratings yet
- Book of News: RSA Conference 2020Document14 pagesBook of News: RSA Conference 2020Jeasson Arce CordovaNo ratings yet
- IT Security Amp Networking 1065934 Euro TrainingDocument4 pagesIT Security Amp Networking 1065934 Euro TrainingHamidNo ratings yet
- The Internet of Things On AWSDocument8 pagesThe Internet of Things On AWSFazlee KanNo ratings yet
- IDS Evaluation GuideDocument12 pagesIDS Evaluation GuideAkash NikhraNo ratings yet
- Smart Protection NetworkDocument2 pagesSmart Protection NetworkIvan Azarel Altamirano CalvarioNo ratings yet
- (IJCST-V11I6P8) :subhadip KumarDocument7 pages(IJCST-V11I6P8) :subhadip KumarEighthSenseGroupNo ratings yet
- Network Detection and Response in The SOC SecuronixDocument7 pagesNetwork Detection and Response in The SOC SecuronixAvo AndrinantenainaNo ratings yet
- Datasheet Lastinfosec 2022Document2 pagesDatasheet Lastinfosec 2022romualdoNo ratings yet
- Project ReportDocument40 pagesProject Reportjarpitha2001No ratings yet
- SophosDocument4 pagesSophoskingheaven722No ratings yet
- Sales FAQ - XDRDocument2 pagesSales FAQ - XDRAlmir KarastanovićNo ratings yet
- Cybersecurity GRC Assessments 1712910184Document14 pagesCybersecurity GRC Assessments 1712910184ellias22 ElliasNo ratings yet
- W - Aaaa14491 (Managed Threat Intelligence - Everything You Need To Know)Document8 pagesW - Aaaa14491 (Managed Threat Intelligence - Everything You Need To Know)Stefano CebrelliNo ratings yet
- Datasheet Brahma (2023)Document8 pagesDatasheet Brahma (2023)Edi ForexNo ratings yet
- CHG - Technical ProposalDocument11 pagesCHG - Technical ProposalJaila Yousri KhalifaNo ratings yet
- Application Security With Automated Threat Modeling and Self ProtectionDocument4 pagesApplication Security With Automated Threat Modeling and Self ProtectionRazafindrabeNo ratings yet
- Final ProjectDocument15 pagesFinal Projectkarlebabu1396No ratings yet
- Cortex Data LakeDocument3 pagesCortex Data Lake1991gabolopezNo ratings yet
- The Journey To XDR Practical Questions To AskDocument6 pagesThe Journey To XDR Practical Questions To AskTan DoNo ratings yet
- Smart Data Cloud Security AllianceDocument49 pagesSmart Data Cloud Security AlliancefewdiscNo ratings yet
- Cybersecurity Analyst RequirementsDocument3 pagesCybersecurity Analyst Requirementsmaximillan njagiNo ratings yet
- BluSapphire DataSheetDocument3 pagesBluSapphire DataSheetMustafa ShaikhNo ratings yet
- Soc, MDR, Edr, NDR and XDRDocument14 pagesSoc, MDR, Edr, NDR and XDRBilal AhmedNo ratings yet
- Percept EDR - Datasheet - 21Document5 pagesPercept EDR - Datasheet - 21Arita DalalNo ratings yet
- Techniques, Solutions and Models Machine Learning Applied To Cybersecurity - Version 1Document4 pagesTechniques, Solutions and Models Machine Learning Applied To Cybersecurity - Version 1Cesar BarretoNo ratings yet
- CySA+ Cheat SheetDocument12 pagesCySA+ Cheat SheetAung Myo KhantNo ratings yet
- Reducing Security Risks of Suspicious Data and Codes Through A Novel Dynamic Defense ModelDocument12 pagesReducing Security Risks of Suspicious Data and Codes Through A Novel Dynamic Defense ModelcalciummNo ratings yet
- Apache MetronDocument15 pagesApache MetronYagnesh BalakrishnanNo ratings yet
- Cortex XDR Whitepaper - CoalfireDocument16 pagesCortex XDR Whitepaper - CoalfireAung Ko ToeNo ratings yet
- Detection and Analysis of Android Ransomware Using The Support Vector MachinesDocument14 pagesDetection and Analysis of Android Ransomware Using The Support Vector Machinesmartin muduvaNo ratings yet
- Neural Networks in Cyber Security: Issue 09, Volume 4 (September 2017)Document4 pagesNeural Networks in Cyber Security: Issue 09, Volume 4 (September 2017)Crazy MechonsNo ratings yet
- Digital Technologies – an Overview of Concepts, Tools and Techniques Associated with itFrom EverandDigital Technologies – an Overview of Concepts, Tools and Techniques Associated with itNo ratings yet
- eresourceERP - Nfra - Proposal - Nirmiti Construction - V1Document29 pageseresourceERP - Nfra - Proposal - Nirmiti Construction - V1amit.andre8144No ratings yet
- Project Plan MPMKVVCLDocument11 pagesProject Plan MPMKVVCLamit.andre8144No ratings yet
- AAI Delivery Enablement Guide v1.8 September 2021Document27 pagesAAI Delivery Enablement Guide v1.8 September 2021amit.andre8144No ratings yet
- Next Gen Data Virtualization EbookDocument12 pagesNext Gen Data Virtualization Ebookamit.andre8144No ratings yet
- Vinsys TNH V 1.0Document24 pagesVinsys TNH V 1.0amit.andre8144No ratings yet
- Oracle EBS Application Enablement For A Leading Tourism CompanyDocument5 pagesOracle EBS Application Enablement For A Leading Tourism Companyamit.andre8144No ratings yet
- Comprehensive EBS Support - Life Insurance CompanyDocument5 pagesComprehensive EBS Support - Life Insurance Companyamit.andre8144No ratings yet
- Streamlining Operations - ERP Solutions For Construction ContractingDocument18 pagesStreamlining Operations - ERP Solutions For Construction Contractingamit.andre8144No ratings yet
- VINSYSDocument12 pagesVINSYSamit.andre8144No ratings yet
- The Impact of AI On LeadershipDocument18 pagesThe Impact of AI On Leadershipamit.andre8144No ratings yet
- Business - Branding - Proposal - Powerpoint - Presentation - Slides UpdatedDocument21 pagesBusiness - Branding - Proposal - Powerpoint - Presentation - Slides Updatedamit.andre8144No ratings yet
- Tenancy Fitout Manual: Gera Developments Pvt. LTDDocument27 pagesTenancy Fitout Manual: Gera Developments Pvt. LTDamit.andre8144No ratings yet
- OCR & PII Data 1Document2 pagesOCR & PII Data 1amit.andre8144No ratings yet
- From Data To DecisionsThe Rise of Predictive Analytics in Decision MakingDocument7 pagesFrom Data To DecisionsThe Rise of Predictive Analytics in Decision Makingamit.andre8144No ratings yet
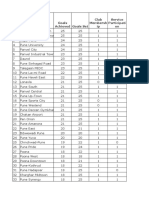
- Goals Set Goals Achieved Club Membersh Ip Service Participati OnDocument20 pagesGoals Set Goals Achieved Club Membersh Ip Service Participati Onamit.andre8144No ratings yet
- 5 Group Evaluation Form TemplateDocument1 page5 Group Evaluation Form Templateamit.andre8144No ratings yet
- Anomaly Detection For XDR Using AIDocument15 pagesAnomaly Detection For XDR Using AIamit.andre8144No ratings yet
- The Next Frontier in AI Autonomous Systems and Their Impact On SocietyDocument6 pagesThe Next Frontier in AI Autonomous Systems and Their Impact On Societyamit.andre8144No ratings yet
- Cloud EngineerDocument20 pagesCloud Engineeramit.andre8144No ratings yet
- Navigating The AI Talent GapDocument8 pagesNavigating The AI Talent Gapamit.andre8144No ratings yet
- Renewal Notice: Policy No.: 30086807202107Document2 pagesRenewal Notice: Policy No.: 30086807202107amit.andre8144No ratings yet
- S. No. District Taluka Village Synergy Club/Co-ordinator Name President Name President Contact NoDocument3 pagesS. No. District Taluka Village Synergy Club/Co-ordinator Name President Name President Contact Noamit.andre8144No ratings yet
- UntitledDocument41 pagesUntitledamit.andre8144No ratings yet
- Tips For Creating A Strong Cybersecurity Assessment ReportDocument1 pageTips For Creating A Strong Cybersecurity Assessment ReportDizzyDudeNo ratings yet
- Karoline Porter Resume 2016Document3 pagesKaroline Porter Resume 2016api-309717062No ratings yet
- What-A-Wonderful-World IPCDocument121 pagesWhat-A-Wonderful-World IPCDonna KellyNo ratings yet
- Book List of Class XiiDocument4 pagesBook List of Class XiiAshish ChaturvediNo ratings yet
- Christ The King College College of Teacher Education Calbayog CityDocument2 pagesChrist The King College College of Teacher Education Calbayog CityRenaline TrinidadNo ratings yet
- Freud 2Document6 pagesFreud 2emmanuel muotchaNo ratings yet
- First AidDocument3 pagesFirst AidDhayu Mart Hindrasyah PandiaNo ratings yet
- Luotion: Date IDocument5 pagesLuotion: Date IJeannette BeriaNo ratings yet
- g7 Hope InventoryDocument3 pagesg7 Hope InventoryRoxanne Jessa CatibogNo ratings yet
- Brain Station 23Document2 pagesBrain Station 23Sree BhowmikNo ratings yet
- Story Board-Learning Facilitator's Schedule For Course 2 ImplementationDocument10 pagesStory Board-Learning Facilitator's Schedule For Course 2 ImplementationNOLLY AMARANNo ratings yet
- StatisticDocument5 pagesStatisticNurul Jannah0% (1)
- GD300 White Paper Project ReportDocument4 pagesGD300 White Paper Project Reportgeary.sutterfield8779No ratings yet
- 10.hum-Evaluation of Learning Activities and Chapter-Chinyere Agatha OmebeDocument8 pages10.hum-Evaluation of Learning Activities and Chapter-Chinyere Agatha OmebeImpact Journals100% (1)
- Edited - GROUP GAMES - COURSE SYLLABUS 1st Sem AY2023 2024Document7 pagesEdited - GROUP GAMES - COURSE SYLLABUS 1st Sem AY2023 2024B09 Kurt Benedict HillNo ratings yet
- Assessment Form For TeachersDocument2 pagesAssessment Form For TeachershinaNo ratings yet
- Thesis PaperDocument37 pagesThesis PapernethNo ratings yet
- Activity Sheet 10.1 Lesson Plan Template - 5E ModelDocument4 pagesActivity Sheet 10.1 Lesson Plan Template - 5E ModelNasyirin FadilahNo ratings yet
- Carl Rogers TheoryDocument24 pagesCarl Rogers TheorySamit RajanNo ratings yet
- Test Driven DevelopmentDocument22 pagesTest Driven DevelopmentMurugan ParamasivanNo ratings yet
- Conflict Across CulturesDocument15 pagesConflict Across CulturesAnkaj MohindrooNo ratings yet
- IT Troubles: Solutions 2nd Edition Upper-IntermediateDocument2 pagesIT Troubles: Solutions 2nd Edition Upper-IntermediateAgo FunesNo ratings yet
- Apex Entrance Exam Test PaperDocument12 pagesApex Entrance Exam Test PaperApex Institute100% (1)